The Infamous Ransomware Akira Group Hits: Quik Pawn Shop in a recent cyber attack, raising concerns about cybersecurity vulnerabilities. To stay ahead of emerging threats, fortify your online security with the HookPhish Dark Web Monitoring platform. Explore HookPhish Dark Web Monitoring.
| Victim Name | Quik Pawn Shop |
| Victim Post Date | 2024-02-22 |
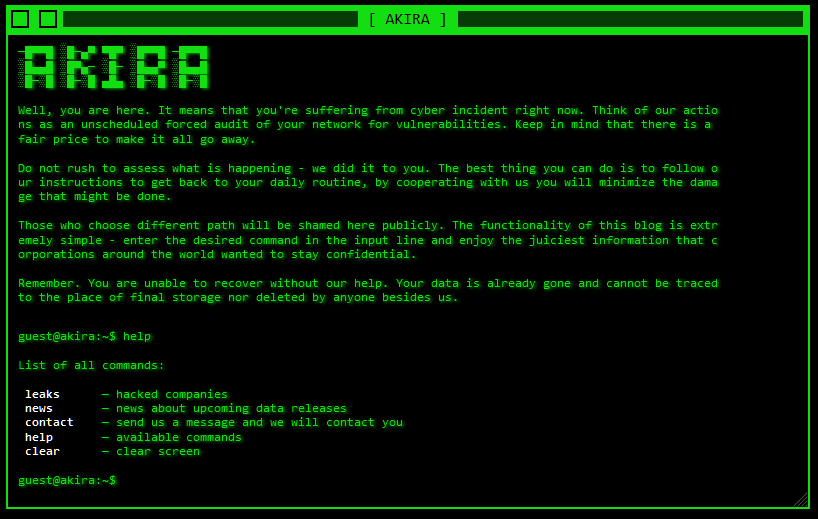
| Description | Founded in 1978, Quik Pawn Shops operates in 15 locations in Mon operates in 15 locations in Montgomery, Birmingham, Mobile and Tuscaloosa areas. We obtained 140 Gb of files of this organization and make them available for you soon. There is also a BD with complete information of their custo mers. Millions of lines with DOB, addresses, ssns, financials tra nsactions and stuff like that. |
Akira Ransomware Group
The ‘Akira’ ransomware group has emerged as a significant threat to businesses, particularly small- and medium-sized organizations in North America and Australia. The group has been known to target the government sector and has been involved in various high-profile attacks. Akira ransomware group’s tactics have evolved over time, with the group shifting its focus from deploying ransomware to exfiltrating sensitive data from victims’ environments. The group has been observed to breach systems by gaining unauthorized access to target organizations’ VPNs, typically through compromised login credentials.
Citations:
- [1] https://scmagazine.com/resource/akira-ransomware-groups-changing-tactics-what-you-need-to-know
- [2] https://scmagazine.com/brief/escalating-akira-ransomware-attacks-target-finland
- [3] https://news.sophos.com/en-us/2023/12/21/akira-again-the-ransomware-that-keeps-on-taking/
- [4] https://provendata.com/blog/akira-ransomware/
- [5] https://trendmicro.com/vinfo/us/security/news/ransomware-spotlight/ransomware-spotlight-akira
Disclaimer: HookPhish does not engage in the exfiltration, downloading, taking, hosting, viewing, reposting, or disclosure of any files or stolen information. Any legal concerns regarding the content should be directed at the attackers, not HookPhish. This blog is dedicated to posting editorial news, alerting readers about companies falling victim to ransomware attacks. HookPhish has no affiliation with ransomware threat actors or groups, and it does not host infringing content. The information on this page is automatically generated and redacted, sourced directly from the Onion Dark Web Tor Blogs pages.